WordPress Two Factor Authentication (CMAUTH) - Use Case - How to Create 2FA Login to Your Site With Google Authenticator
Use Case - How to create 2FA login to your site with Google Authenticator
Note: This guide requires:
- WordPress Two Factor Authentication – This document uses version 1.6.7.
Video Use-Case
Introduction
WordPress Two Factor Authentication rebuilds the account security for your WordPress users by offering integration with four widely accredited two-factor authentication (2FA) methods: Google Authenticator, Mobile Phone SMS, Email verification and Email code. By not relying on the password alone, users feel confident that their credentials and data are stored safely.
Use Case Front-End

Use Case Assumptions
In this example use case guide we will consider how to create 2FA login to your site with Google Authenticator.
Google Authenticator is an application for smartphones that works with third party software. Users must insert a code that is dynamically generated in the application to access their account. The application is available for Android devices and iOS devices.
During the first use, it's necessary to link the app and account either through a QR Code or a secret key. Google provides a step-by-step guide about this.
It follows:
- Installing the plugin
- General settings
- Google Authenticator
- Individual user settings
- IPs and devices restrictions
- Appearance
- Labels
- End Result
Installing the Plugin
The process is the same for all CM plugins and add-ons.
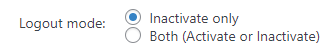
- Download the plugin from your customer dashboard.
- Log in to WordPress and navigate to the WordPress Admin → Plugins settings.
- Click on Add New.
- Activate it and add the license.
Learn more: Getting Started - Plugin Overview
General Settings
Enabling Google Authenticator protection on your site is quite simple. To configure all base options you need to navigate to Admin Dashboard → CM Secure Login Pro → Settings → General tab.
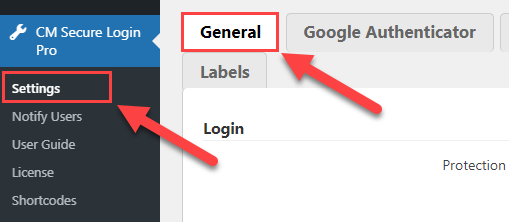
There you can find a few sections with the options. Let's consider the ones that are important for configuring Google Authenticator protection.
Login
-
Protection method - This option is a core of the plugin. Here you need to choose which protection method you want to use. You can choose from four protection methods: Google Authenticator, Email verification code, Email confirmation link, SMS verification code. You can also let users choose between SMS code and e-mail code. In this use case we choose Google Authenticator method.

Choosing protection method Other Protection Methods
Learn more about other protection methods in these use cases:
-
Require chosen protection method for all users - Enable this option if you want to apply the previously selected solution for all users.

Choose if to require chosen protection method for all users -
Require chosen protection method for chosen roles - If previous option is disabled, you can apply chosen protection method only for definite user roles that you can choose in the list.

Requiring chosen protection method for specific user roles TIP: Notify Users
You can notify your users about the changes in login process by sending them emails. You can learn more about how to do it in this guide: WordPress Two Factor Authentication (CMAUTH) - How To - Notify Users About Login Process Changes
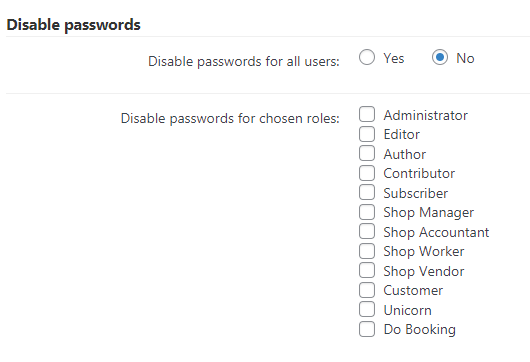
Disable passwords
You can disable the password for every user or only for those with certain roles. Note that disabling the password does not mean the users will only need their username to sign in. Instead, they will login with their usernames and the chosen authentication method.
- Disable passwords for all users - Choose Yes to disable passwords for all users.
- Disable passwords for chosen roles - Choose here roles that won't need to use password for login. Works if previous option is disabled (chosen No).
Common
Here you can configure additional security options.
-
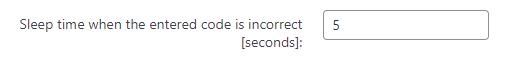
Sleep time when the entered code is incorrect [seconds] - Set a delay time to send to the browser if a user enters an invalid code from Google Authenticator or e-mail. This can slow down malicious bots which try to login using the brute-force method.
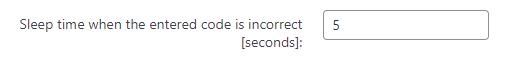
Specifying sleep time when the entered code is incorrect -
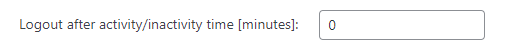
Logout after activity/inactivity time [minutes] - Users will be logged out after this period of activity/inactivity (in minutes). Set to 0 to disable.
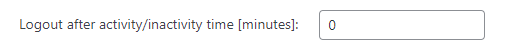
Specifying logout time -
Logout mode - Here you can choose in which cases to logout the users: after some period of inactivity, or in both cases - activity and inactivity. Works if previous option is enabled.
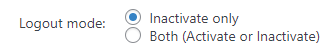
Choosing logout mode
Google Authenticator
Next important tab is Google Authenticator.
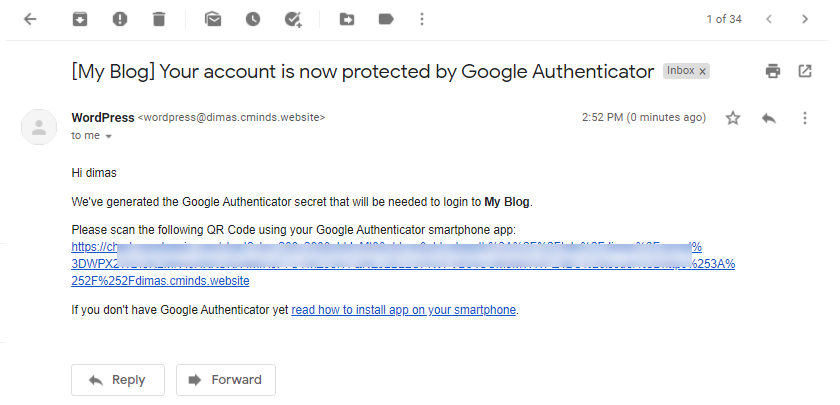
In this tab, you can edit the template for two kinds of email:
-
Created secret email template - Email for when the Google Authenticator is first set to the account.

Created secret email template -
Remind secret email template - Email for when users have misplaced their secret key.

Remind secret email template
You can use the following shortcodes to add dynamic content to subject and body of these emails:
- Subject shortcodes:
- [blogname]
- [siteurl]
- [userdisplayname]
- [userlogin]
- [useremail]
- Body shortcodes:
- [link] - link to the QR Code with secret. Note: this shortcode must be in the email.
- [blogname]
- [siteurl]
- [userdisplayname]
- [userlogin]
- [useremail]
Result
Base configuration is done, so don't forget to click the button Save at the bottom of the page, and let's check how it works on the front-end.
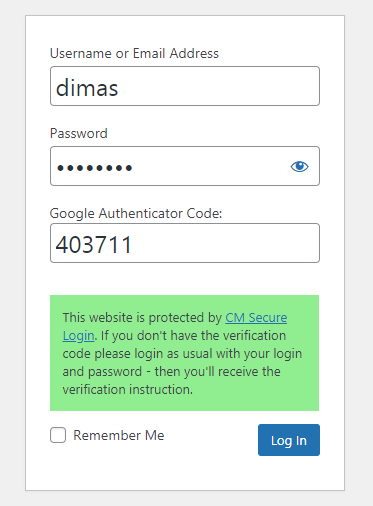
When the user tries to login for the first time after 2FA is enabled, he needs to login as usual - by entering his username/email and password.
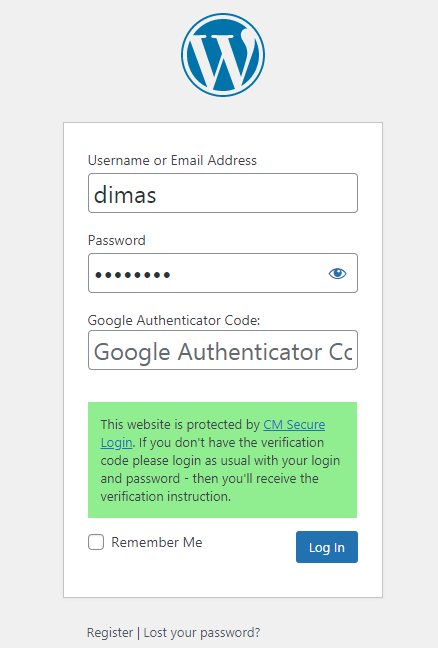
He will be notified that GA secret was sent to his email.
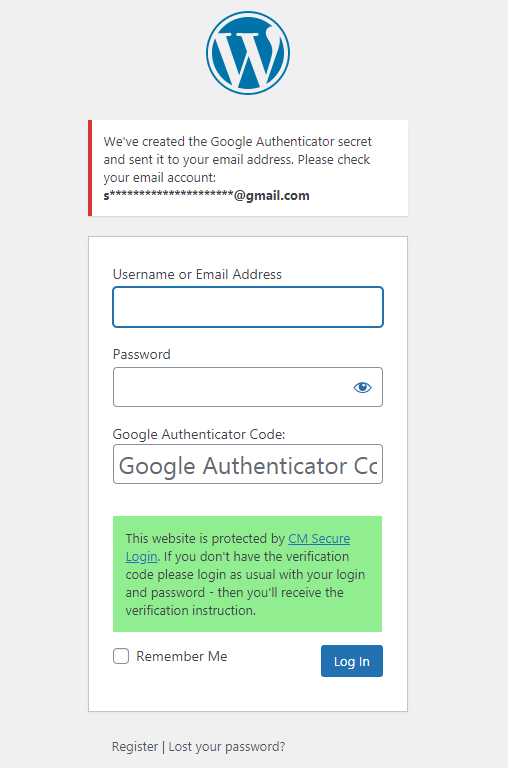
In the email the user needs to click the provided link and then scan QR code using GA app on his phone.
And then login using his username/email, password and one-time password from GA app.
Individual User Settings
WordPress Two Factor Authentication allows you to apply the chosen secure method not only to all users or specific roles, but also allows you to change settings specifically to each user.
To do this, navigate to Admin Dashboard → Users → All Users.
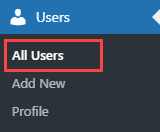
Hover on the needed user and click Edit.
You will see the following panel in the user's page:

On the screenshot above you can see an example of the panel for the user that belongs to the user role with enabled 2FA protection. It works the same for the user roles with disabled 2FA protection.
The options are:
- Disable/enable protection - Either turns the 2FA on or off for this user.
- Reset secret / Show secret / Send secret by email - Valid for Google Authenticator only.
- Clear admin decision - Resets any individual changes in favor of global settings.
IPs and Devices Restrictions
There are a few more features for additional security of the accounts.
To configure them get back to Admin Dashboard → CM Secure Login Pro → Settings.
IP
First tab we need - IP.
You can choose how many IP addresses are allowed for each user role.
The options are:
- Restrict user IPs - Enables the feature.
- User roles affected by IPs restriction - Mark which roles will be affected.
- Maximum of IPs allowed to each user - Choose a number (1 or higher).
- Accept only IPs chosen by the admin - Only allows logins from specific IPs defined by the admin per each user. This means that login attempts from other IPs will be blocked even if more IPs slots are available.

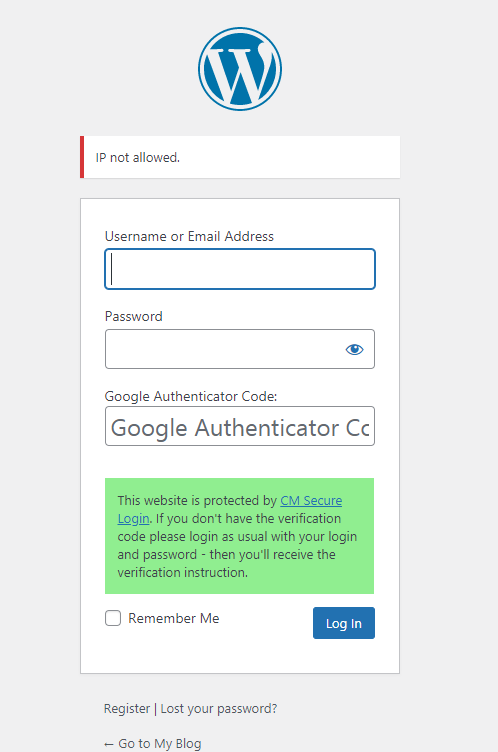
In result, if someone tries to login to the account from new IP, and IPs limit is reached, or this IP is not allowed by the admin, there will be a following message:
Learn more about IPs restrictions in this guide: WordPress Two Factor Authentication (CMAUTH) - How To - Restrict User Login By Number of IPs
Device
Another tab we need - Device.
You can restrict certain user roles from logging in from too many different devices.
- Restrict user devices - Enables the feature.
- Select user roles with devices restricting - Mark which roles will be affected.
- Maximum number of devices allowed to user - Choose a number (1 or higher).
In result, if someone tries to login to the account from new device, and devices limit is reached, there will be a following message:
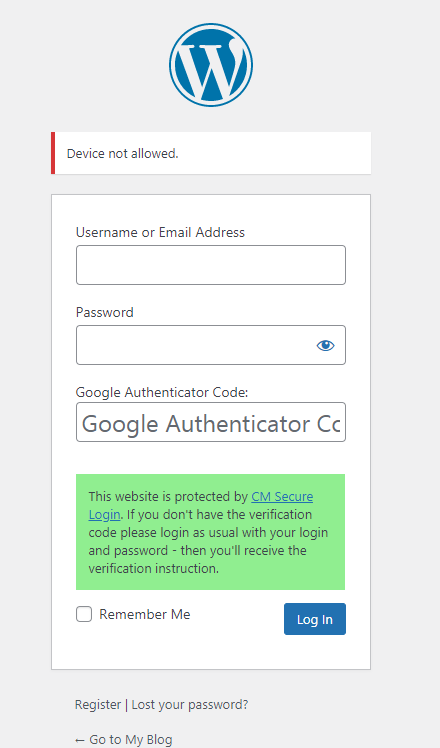
Learn more about devices restrictions in this guide: WordPress Two Factor Authentication (CMAUTH) - How To - Restrict User Login By Number of Devices
Appearance
On the Appearance tab you can add and change instructions and modify the appearance of the login form with CSS.
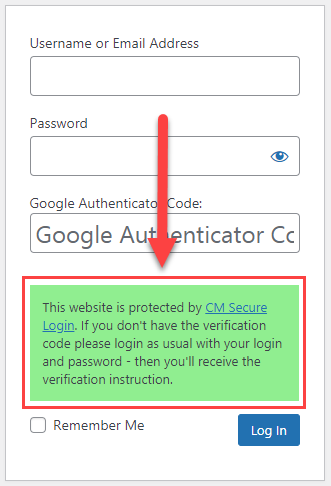
- Enable login instructions - Enables this option.
- Login instructions content - Enter the login instructions that will be displayed on the login form.
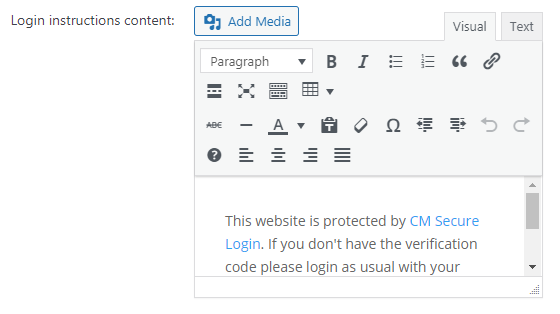
- Custom CSS - To further personalize your form, you can insert custom CSS. It will affect the following hooks: wp_head, admin_head, login_head.
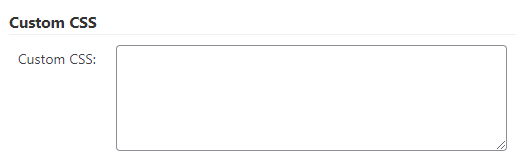
Labels
On the Labels tab you can change the text of every label on the front-end. This feature is especially useful for localizing the form to different languages.
Google Authenticator labels:
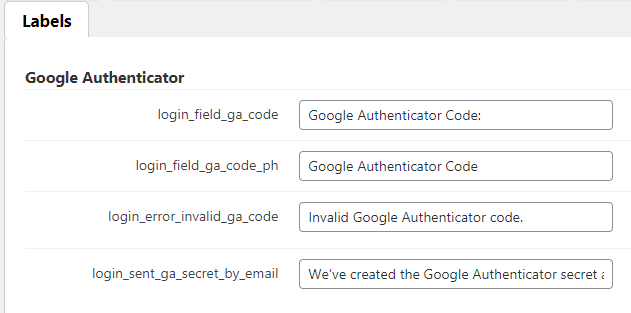
IPs and Devices restriction labels:
End Result
Following instructions found in the plugin and guides, you should be able to create 2FA login to your site with Google Authenticator.
Use Case Front-End

 |
More information about the WordPress Two Factor Authentication plugin Other WordPress products can be found at CreativeMinds WordPress Store |
 |
Let us know how we can Improve this Product Documentation Page To open a Support Ticket visit our support center |